Categories
- animatronics (12)
- apple (11)
- arduino (179)
- art (41)
- articles (121)
- artificial intelligence (11)
- automation (421)
- avr (205)
- bitcoin (3)
- breadboard (9)
- cameras (57)
- cars (26)
- cell phones (28)
- clothing mods (21)
- console mods (26)
- dangerous (94)
- desktop mods (24)
- embedded (5)
- flying things (54)
- fpga (22)
- gaming creations (108)
- interface (225)
- internet (17)
- laptop mods (6)
- lasers (22)
- linux (7)
- magnetic (3)
- medical (12)
- microcontrollers (51)
- misc projects (152)
- msp (12)
- music (124)
- pic (90)
- projects (23)
- pyroedu (76)
- raspberry pi (26)
- robots (312)
- security (36)
- sensors (307)
- software (200)
- solar (19)
- stamp (9)
- tools (149)
- tutorials (98)
- Uncategorized (45)
- usb (44)
- wireless (256)
Sponsors


Posted July 14, 2015 by Chris
"The Senior Year Design Project was named Vanguard by the team. He is a remote controlled surveillance robot. To avoid data communication problems we decided to use different protocols for controlling the wireless camera and the robot. The robot can be controlled through desktop or laptop computers while the video can be controlled through internet, adhoc, WAN and LAN. It is powered by two batteries. One for the circuit and one for its motors."
Posted July 9, 2015 by Chris
"In this short article, I present a nifty technique for promiscuously sniffing such radios by (1) limiting the MAC address to 2 bytes, (2) disabling checksums, (3) setting the MAC to be the same as the preamble, and (4) sorting received noise for valid MAC addresses which may later be sniffed explicitly."

Posted May 11, 2015 by Chris
"KeySweeper is a stealthy Arduino-based device, camouflaged as a functioning USB wall charger, that wirelessly and passively sniffs, decrypts, logs and reports back (over GSM) all keystrokes from any Microsoft wireless keyboard in the vicinity."

Posted February 28, 2015 by Chris
"The key I made works beautifully both on my garage door, as well as on a number of other readers I tried. I have decided to publish this, as more people should be aware of the design flaws that are inherent in older RFID implementations, and to allow others to make their own universal key."
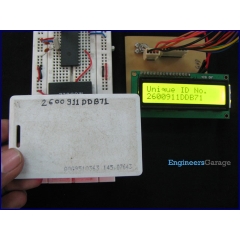
Posted February 19, 2015 by Chris
"By employing RFID, secure entry systems can be developed without incurring huge costs. These are the reasons of excessive use of RFID technology. In this article, interfacing of an RFID reader module has been explained with PIC18F4550. The USART interrupt, an internal PIC interrupt, has also been explained."

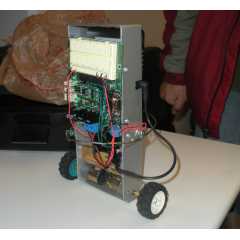
Posted February 14, 2014 by Chris
"The purpose of the prototype was to demonstrate the feasibility of a small, highly maneuverable search and rescue robot. As such, the completed prototype was successful. Capabilities include a ground speed of 10 inches per second, battery life of 50 minutes, wireless range of between 50 and 150 feet, weight of 14.5 pounds and the ability to climb stairs."

Posted December 16, 2013 by Chris
"This paper presents the design, implementation, and evaluation of the RFID Guardian, the first-ever unified platform for RFID security and privacy administration. The RFID Guardian resembles an ‘RFID firewall,’ that monitors and controls access to RFID tags by combining a standard-issue RFID reader with unique RFID tag emulation capabilities."
Posted July 31, 2013 by Chris
“EGGN 482: Microprocessor and microcontroller architecture focusing on hardware structures and elementary machine and assembly language programming skills essential for use of microprocessors in data acquisition, control, and instrumentation systems. Analog and digital signal conditioning, communication, and processing. A/D and D/A converters for microprocessors. RS232 and other communication standards.”

Posted June 28, 2013 by Chris
“GSM Home Security is a project to monitor the home when you are out of the house through the GSM network. The project uses four magnetic switches installed on any door in the house to trigger notification of doors being open or closed.”
Posted February 24, 2013 by Chris
“This project seeks to develop an additional form of authentication for vehicle security, specifically in the form of a tapped password. The goal of this project is to implement this form of authentication and determine the level of possible security while maintaining enough flexibility to allow human variation in password inputs.”